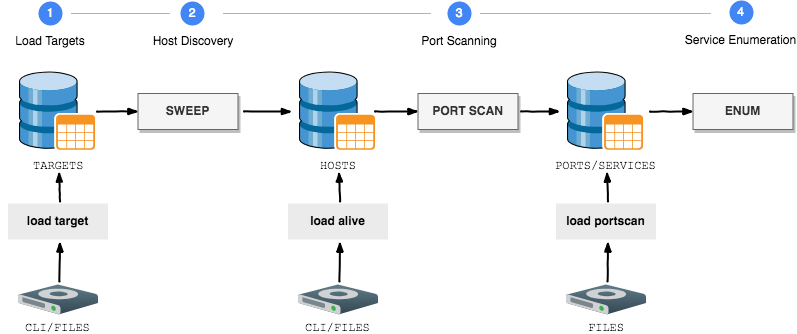
GoScan is an interactive network scanner client, featuring auto-completion, which provides abstraction and automation over nmap.
GoScan can now be used to perform host discovery, port scanning, and service enumeration not only in situations where being stealthy is not a priority and time is limited (think at CTFs, OSCP, exams, etc.), but also (with a few tweaks in its configuration) during professional engagements.
GoScan is also particularly suited for unstable environments (think unreliable network connectivity, lack of “screen“, etc.), given that it fires scans and maintain their state in an SQLite database.
Scans run in the background (detached from the main thread), so even if connection to the box running GoScan is lost, results can be uploaded asynchronously (more on this below).
That is, data can be imported into GoScan at different stages of the process, without the need to restart the entire process from scratch if something goes wrong.
In addition, the Service Enumeration phase integrates a collection of other tools (e.g., EyeWitness, Hydra, nikto, etc.), each one tailored to target a specific service.
Also Read : Fnord : Pattern Extractor for Obfuscated Code
Installation
Binary installation (Recommended)
Linux (64bit)
$ wget https://github.com/marco-lancini/goscan/releases/download/v2.3/goscan_2.3_linux_amd64.zip
$ unzip goscan_2.3_linux_amd64.zip
Linux (32bit)
$ wget https://github.com/marco-lancini/goscan/releases/download/v2.3/goscan_2.3_linux_386.zip
$ unzip goscan_2.3_linux_386.zip
After that, place the executable in your PATH
$ chmod +x goscan
$ sudo mv ./goscan /usr/local/bin/goscan
Build from source
$ git clone https://github.com/marco-lancini/goscan.git
$ cd goscan/goscan/
$ make setup
$ make build
To create a multi-platform binary, use the cross command via make:
$ make cross
Docker
$ git clone https://github.com/marco-lancini/goscan.git
$ cd goscan/
$ docker-compose up –build
Usage
GoScan supports all the main steps of network enumeration:
| Step | Commands |
|---|---|
| 1. Load targets | Add a single target via the CLI (must be a valid CIDR): load target SINGLE <IP/32>Upload multiple targets from a text file or folder: load target MULTI <path-to-file> |
| 2. Host Discovery | Perform a Ping Sweep: sweep <TYPE> <TARGET> Or load results from a previous discovery:Add a single alive host via the CLI (must be a /32): load alive SINGLE <IP>Upload multiple alive hosts from a text file or folder: load alive MULTI <path-to-file> |
| 3. Port Scanning | Perform a port scan: portscan <TYPE> <TARGET>Or upload nmap results from XML files or folder: load portscan <path-to-file> |
| 4. Service Enumeration | Dry Run (only show commands, without performing them): enumerate <TYPE> DRY <TARGET> Perform enumeration of detected services: enumerate <TYPE> <POLITE/AGGRESSIVE> <TARGET> |
| 5. Special Scans | EyeWitnessTake screenshots of websites, RDP services, and open VNC servers (KALI ONLY): special eyewitnessEyeWitness.py needs to be in the system pathExtract (Windows) domain information from enumeration dataspecial domain <users/hosts/servers>DNSEnumerate DNS (nmap, dnsrecon, dnsenum): special dns DISCOVERY <domain>Bruteforce DNS: special dns BRUTEFORCE <domain>Reverse Bruteforce DNS: special dns BRUTEFORCE_REVERSE <domain> <base_IP> |
| Utils | Show results: show <targets/hosts/ports>Automatically configure settings by loading a config file: set config_file <PATH>Change the output folder (by default ~/goscan): set output_folder <PATH>Modify the default nmap switches: set nmap_switches <SWEEP/TCP_FULL/TCP_STANDARD/TCP_VULN/UDP_STANDARD> <SWITCHES>Modify the default wordlists: set_wordlists <FINGER_USER/FTP_USER/...> <PATH> |
External Integrations
The Service Enumeration phase currently supports the following integrations:
| WHAT | INTEGRATION |
|---|---|
| ARP | nmap |
| DNS | nmapdnsrecondnsenumhost |
| FINGER | nmapfinger-user-enum |
| FTP | nmapftp-user-enumhydra [AGGRESSIVE] |
| HTTP | nmapniktodirbEyeWitnesssqlmap [AGGRESSIVE]fimap [AGGRESSIVE] |
| RDP | nmapEyeWitness |
| SMB | nmapenum4linuxnbtscansamrdump |
| SMTP | nmapsmtp-user-enum |
| SNMP | nmapsnmpcheckonesixtyonesnmpwalk |
| SSH | hydra [AGGRESSIVE] |
| SQL | nmap |
| VNC | EyeWitness |








