APPLICATIONS
HOT NEWS
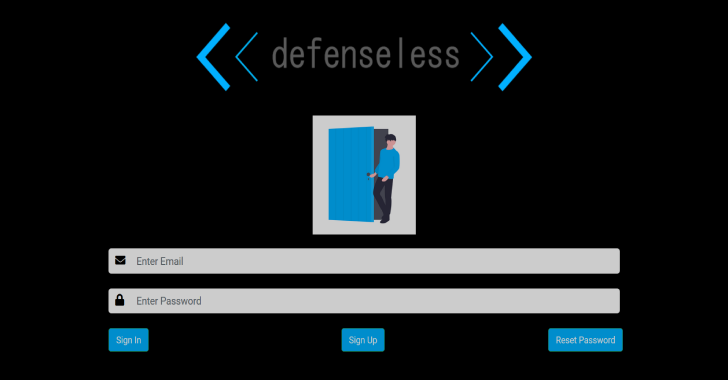
defenselessV1 : Just Another Vulnerable Web Application
defenselessV1 is a vulnerable web application written in PHP/MySQL. This is the first version of this application. The purpose of this application is...
© kalilinuxtutorials.com 2025