APPLICATIONS
HOT NEWS
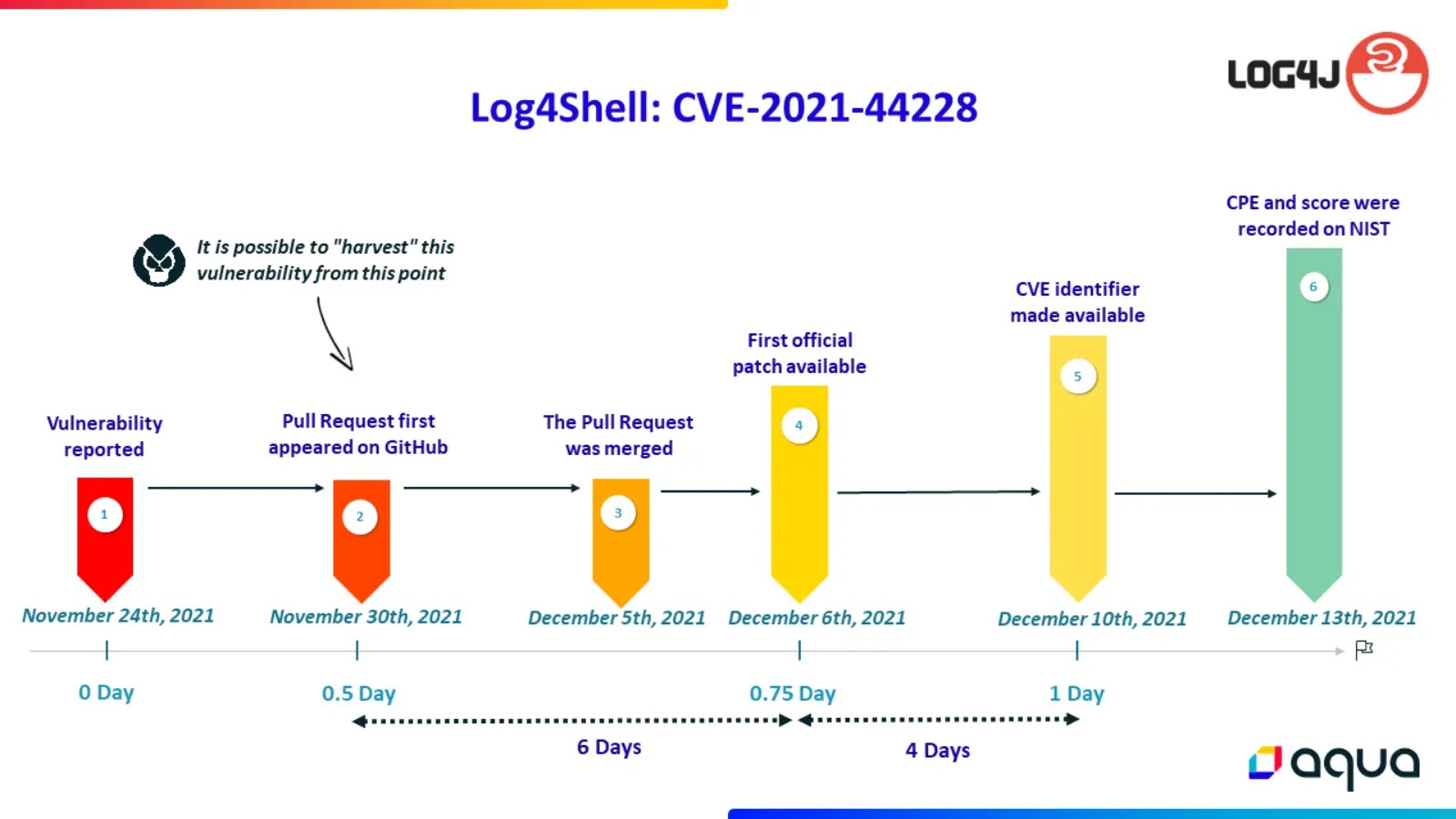
CVE Half-Day Watcher
CVE Half-Day Watcher is a security tool designed to highlight the risk of early exposure of Common Vulnerabilities and Exposures (CVEs) in the public...
© kalilinuxtutorials.com 2025