Windows services are essential components that run in the background to perform various tasks. The sc.exe utility, a command-line tool included in Windows, allows users to create or modify these services.
By specifying the binpath parameter, administrators can define the executable or binary that the service will run. This capability makes sc.exe a versatile tool for system management but also a potential vector for abuse by threat actors.
Creating A New Service
To create a new Windows service using sc.exe, the create command is used along with the binpath parameter. The syntax is as follows:
sc.exe create <ServiceName> binpath= "<PathToExecutable>" [options]For example:
sc.exe create MyService binpath= "C:\Path\To\Executable.exe" start= autoHere:
binpath=specifies the path to the executable that the service will run.start=defines how the service starts (e.g.,auto,demand, ordisabled).
Additional parameters can set dependencies, account credentials, and display names for better service management.
Modifying An Existing Service
The config command in sc.exe allows modification of an existing service’s properties, including its binpath. For example:
sc.exe config MyService binpath= "C:\New\Path\To\Executable.exe"This updates the executable path for the specified service without deleting or recreating it. Other options, such as changing the start type or error severity, can also be configured.
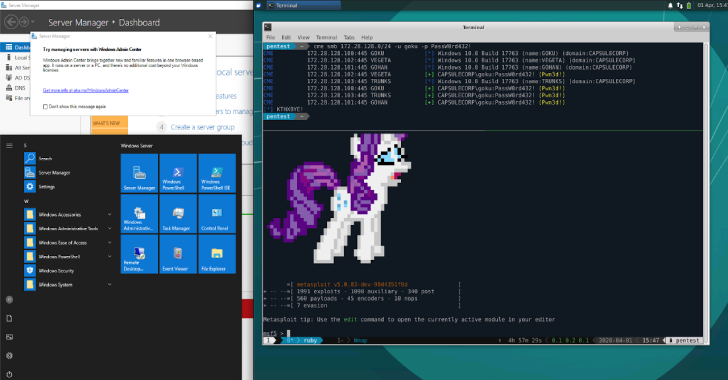
Threat actors often exploit Windows services for persistence or privilege escalation. By creating or modifying services with malicious binaries via binpath, attackers can execute arbitrary code with elevated privileges.
Monitoring for suspicious use of sc.exe commands is crucial in detecting such activities.
Organizations can use tools like Microsoft Defender for Endpoint to monitor commands involving sc.exe and detect unusual paths in the binpath. Queries such as:
DeviceProcessEvents
| where InitiatingProcessFileName =~ "cmd.exe"
| where FileName =~ "sc.exe"
| where ProcessCommandLine has_any ("create","config")
| where ProcessCommandLine has "binpath"help identify potentially malicious service creation or modification events.
By combining proactive monitoring with strict access controls, administrators can mitigate risks associated with unauthorized use of sc.exe.








.jpg)