APPLICATIONS
HOT NEWS
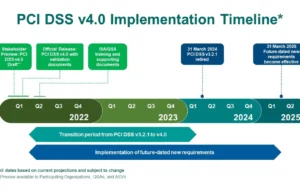
PCI-SegTest : Streamlining PCI DSS v4.0 Compliance Through Advanced Network Segmentation...
The "PCI-SegTest" tool is a specialized utility designed to ensure compliance with PCI DSS v4.0 by testing network segmentation and egress controls within the...
© kalilinuxtutorials.com 2025






.png)
.png)
.png)
.png)

.png)
.png)
.png)