APPLICATIONS
HOT NEWS
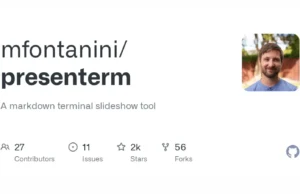
Presenterm : Revolutionizing Terminal-Based Presentations With Markdown
presenterm lets you create presentations in markdown format and run them from your terminal, with support for image and animated gifs, highly customizable themes,...
© kalilinuxtutorials.com 2025