APPLICATIONS
HOT NEWS
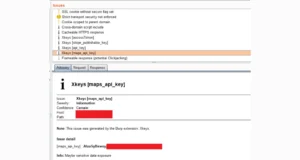
ReelPhish – A Real-Time Two-Factor Phishing Tool
ReelPhish is a real-time two-factor phishing tool. This ReelPhish tool has been released along with a FireEye blog post. The blog post can be...
© kalilinuxtutorials.com 2025