APPLICATIONS
HOT NEWS
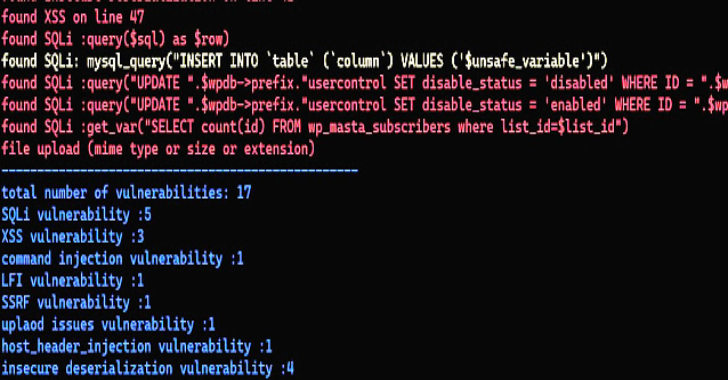
Php_Code_Analysis : Scan your PHP code for vulnerabilities
Php_Code_Analysis is a tool to Scan your PHP code for vulnerabilities
the script can find
check_file_upload issueshost_header_injectionSQl injectioninsecure deserializationopen_redirectSSRFXSSLFIcommand_injection
Features
fastsimple report
Usage
python code.py >>> this will scan...
© kalilinuxtutorials.com 2025