Getsploit allows you to search online for the exploits across all the most popular collections: Exploit-DB, Metasploit, Packetstorm and others. The most powerful feature is immediate exploit source download right in your working path.
Utility was tested on a python2.6, python2.7, python3.6 with SQLite FTS4 support. If you have found any bugs, don’t hesitate to open issue.
Also Read Spykeyboard – Keylogger Which Sends Us The Data To Our Gmail
How To Use Getsploit ?
Installation
pip install getsploit
Search
# git clone https://github.com/vulnersCom/getsploit
# cd getsploit
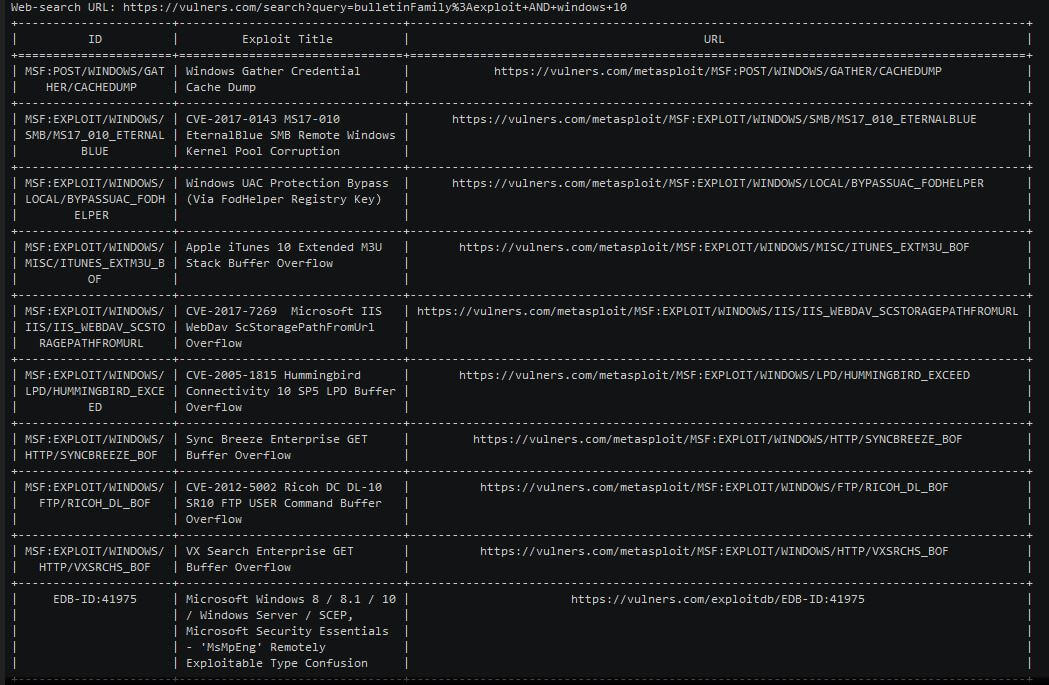
# ./getsploit.py wordpress 4.7.0
Total found exploits: 8
Web-search URL: https://vulners.com/search?query=bulletinFamily%3Aexploit%20AND%20wordpress%204.7.0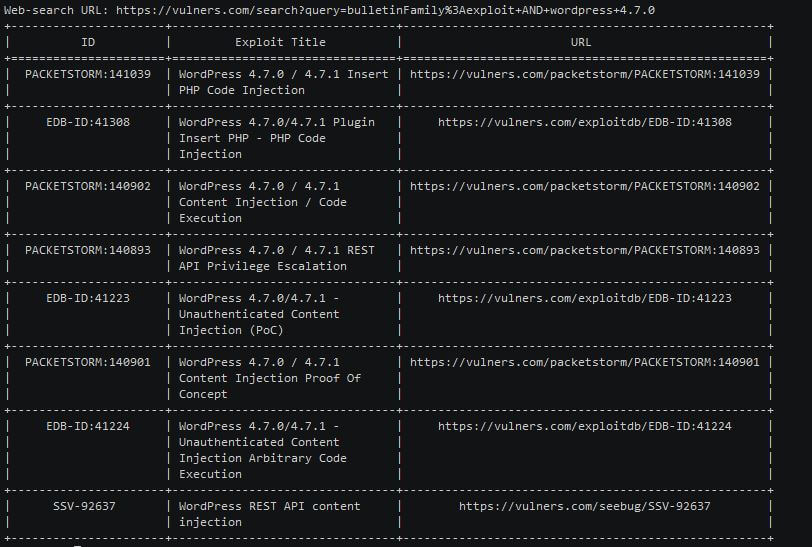
Save exploit files
# ./getsploit.py -m wordpress 4.7.0
Total found exploits: 8
Web-search URL: https://vulners.com/search?query=bulletinFamily%3Aexploit%20AND%20wordpress%204.7.0Local Database
If your Python supports sqlite3 lib(builtin) you can use –update and –local commands to download whole exploit database to your PC. After update you can perform local offline searches.
# ./getsploit.py --update
Downloading getsploit database archive. Please wait, it may take time. Usually around 5-10 minutes.
219642496/219642496 [100.00%]
Unpacking database.
Database download complete. Now you may search exploits using --local key './getsploit.py -l wordpress 4.7'








%20(1).png)
.png)