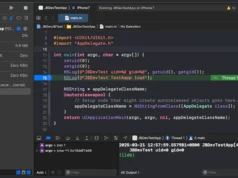
PatchlessCLRLoader is a fork of InlineExecute-Assembly to load .NET assembly and direct the output to mailslot. I rewrites it to a standalone loader with the following implementation:
- AES encryption payload
- Fileless payload support
- Patchless AMSI and ETW bypass using hardware breakpoint
Remarks:The loader only supports setting HWBP in main thread currently.
Using hardware breakpoints for patchless bypass has multiple advantages over traditional patching techniques.
Firstly, it avoids using widely-known APIs such as NtProtectVirtualMemory, which are closely monitored by security solutions.
Secondly, hardware breakpoints do not require any modification to the files, which could be detected by file integrity monitoring or EDR, resulting in a relatively stealthy approach.
Execute
PatchlessCLRLoader.exe <payload> <key> <arguments>Bug
The process may hang due to an access violation during CLR, but this issue can be overcome by using output function of the loaded .NET assembly, if it is supported. (e.g. -outputfile of Seatbelt). Pending Fix.








.webp)

