“RustRedOps” stands as a groundbreaking repository, pioneering the development of sophisticated Red Team tools and techniques, all crafted in the Rust programming language.
It offers a comprehensive suite of projects aimed at enhancing security assessments and intrusion testing for professionals.
This article delves into the rich array of tools available, from APC injection to encryption and anti-debugging, showcasing the power and flexibility of Rust in cybersecurity operations.
Summary
- In Construction
- Overview
- Contents
- Resources
- Requirements
- Compile
- Compiling the Project
- Adding Destination Architectures
- Compiling for a Specific Architecture
- How to get started
- Contributing to RustRedOps
- Credits / References / Thanks / Motivation
In Construction
The project is still under development
Overview
RustRedOps is a repository that houses various tools and projects related to Red Team operations, developed in Rust.
This repository is dedicated to providing effective and efficient tools for security professionals and penetration testers who want to perform security assessments and intrusion tests.
Contents
The repository is organized into several projects, each with its own purpose and functionality. Here are some examples of the projects included:
- APC Injection
- This project exploits the Asynchronous Code Injection (APC) technique to execute malicious code in target processes.
- Early Bird APC Injection
- It focuses on a variation of APC injection, executing code before the main process starts.
- Local Payload Execution
- This project addresses the direct execution of malicious payloads in a system’s local environment.
- Process Argument Spoofing
- Exploits the technique of masking or altering the arguments of a process to hide malicious activity.
- Process Injection (DLL)
- It focuses on injecting dynamic link libraries (DLL) into running processes to execute malicious code.
- Process Injection (Shellcode)
- It exploits shellcode injection directly into running processes to control or execute malicious tasks.
- Local Thread Hijacking
- This project deals with hijacking the threads of processes running on the local system to execute malicious code.
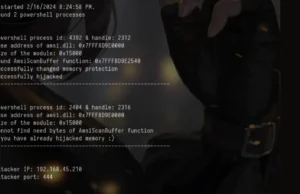
- Remote Thread Hijacking
- It addresses the hijacking of threads in remote system processes to carry out malicious actions.
- Local Function Stomping Injection
- It focuses on replacing locally running functions with malicious code, changing their default behavior.
- Remote Function Stomping Injection
- It exploits the substitution of functions in remote systems to carry out malicious activities.
- Local Mapping Injection
- Performing malicious code injection via memory mapping into local processes.
- Remote Mapping Injection
- Performing malicious code injection via memory mapping into remote processes.
- Minidump-rs
- Dumping the lsass.exe process.
For more information click here.





.webp)

.jpg)