APPLICATIONS
HOT NEWS
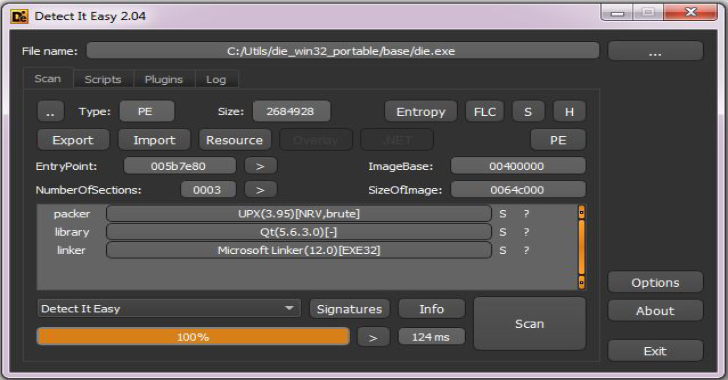
DIE : Program For Determining Types Of Files For Windows, Linux...
Detect It Easy, or abbreviated DIE is a program for determining types of files. It is a cross-platform application, apart from Windows version there...
© kalilinuxtutorials.com 2025