APPLICATIONS
HOT NEWS
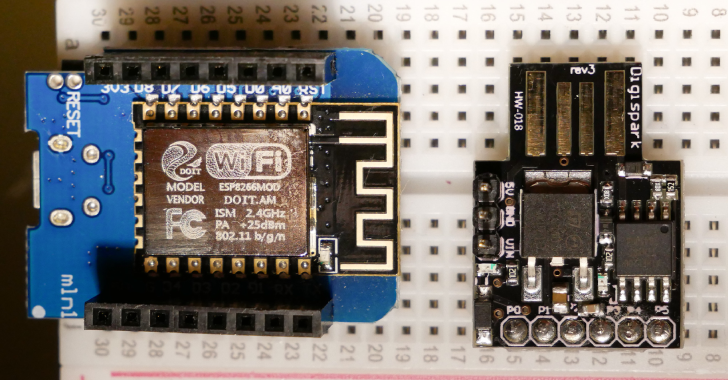
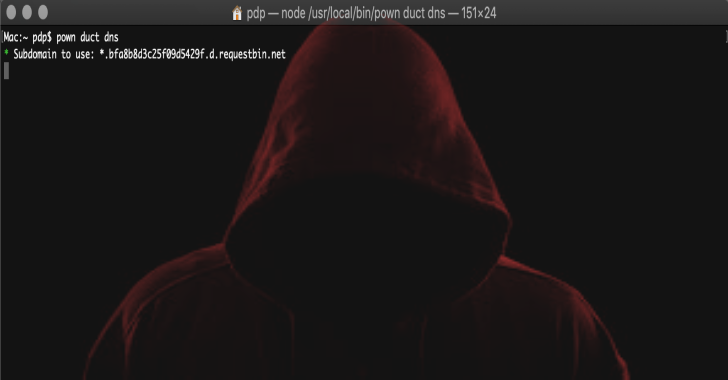
GIVINGSTORM : Infection Vector That Bypasses AV, IDS, & IPS
GIVINGSTORM is a breeze to use. Simply clone the directory, and cd into it. The beginnings of a C2 framework. Currently without all the...
© kalilinuxtutorials.com 2025