APPLICATIONS
HOT NEWS
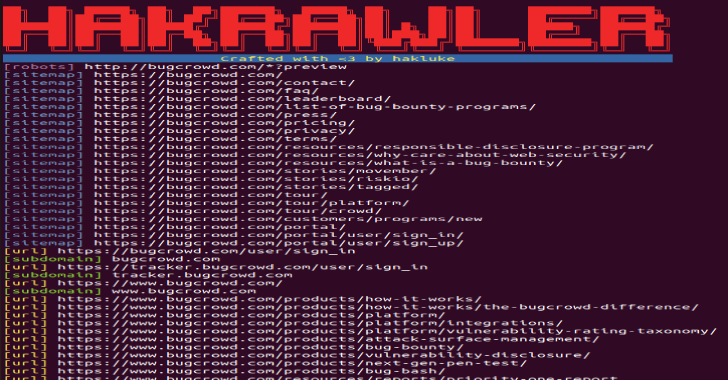
Hakrawler : Discovery Of Endpoints & Assets Within A Web Application
Hakrawler is a Go web crawler designed for easy, quick discovery of endpoints and assets within a web application. It can be used...
© kalilinuxtutorials.com 2025