APPLICATIONS
HOT NEWS
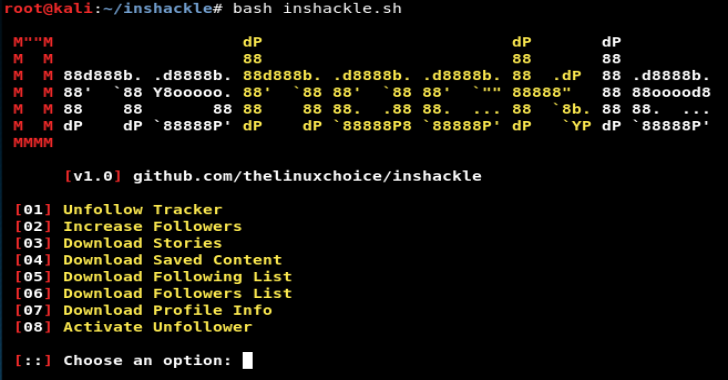
Inshackle : Instagram Hacks
Inshackle is a tool used to hack Instagram and track unfollowers, increase your followers, download Stories, etc.
Features
Unfollow TrackerIncrease FollowersDownload: Stories, Saved Content, Following/followers list,...
© kalilinuxtutorials.com 2025