APPLICATIONS
HOT NEWS
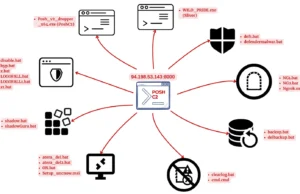
Identifying Accounts Used From A Threat Actor Device
In cybersecurity, identifying accounts accessed by a threat actor's device is a critical aspect of incident response and threat hunting.
This process is particularly...
We provide you with the latest Kali Linux & Penetration testing tools.
Contact us: admin@kalilinuxtutorials.com
© @Kali Linux Tutorials - 2025

















.png)