APPLICATIONS
HOT NEWS
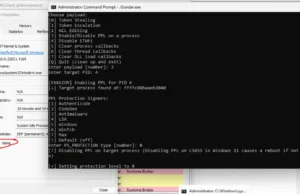
Sunder : A Windows Rootkit Exploiting Vulnerable Drivers For Kernel-Level Attacks
Sunder is a Windows rootkit inspired by the Lazarus Group's FudModule rootkit, designed to exploit vulnerabilities in kernel drivers to gain unauthorized access to...
© kalilinuxtutorials.com 2025











.webp)
.webp)