APPLICATIONS
HOT NEWS
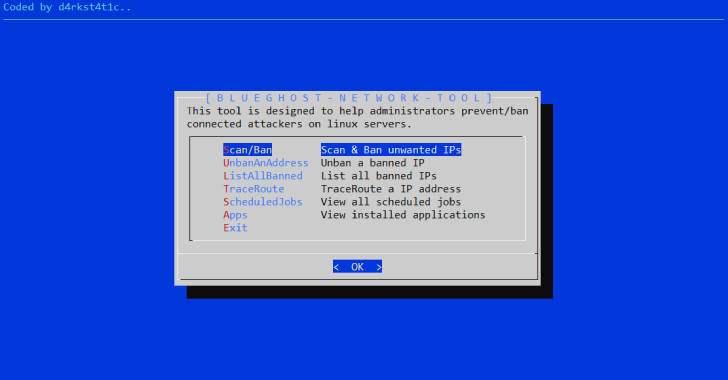
BlueGhost : Network Tool Designed To Assist Blue Teams In Banning...
BlueGhost tool utilises various Linux network tools and bash scripting to assist blue teams on defending Debian and Ubuntu based servers from malicious attackers. ...
© kalilinuxtutorials.com 2025