APPLICATIONS
HOT NEWS
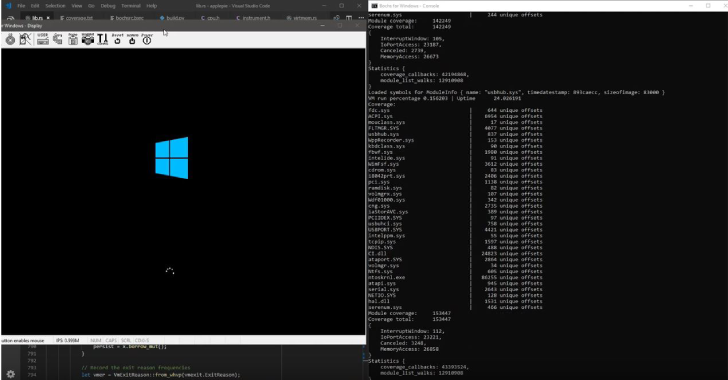
Applepie : A Hypervisor For Fuzzing Built With WHVP & Bochs
Hello! Welcome to applepie! This is a tool designed for fuzzing, introspection, and finding bugs! This is a hypervisor using the Windows Hypervisor Platform...
© kalilinuxtutorials.com 2025