APPLICATIONS
HOT NEWS
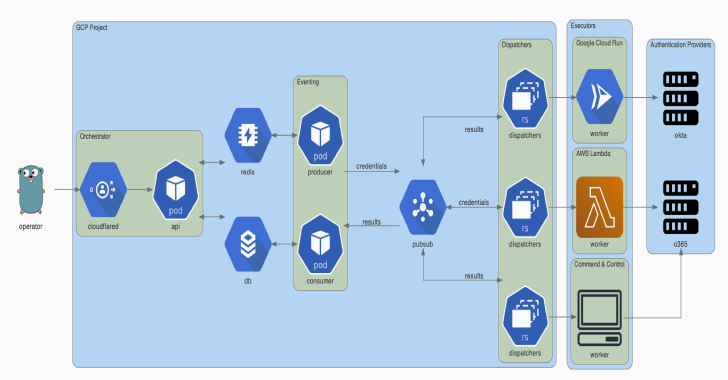
Trident : Automated Password Spraying Tool
The Trident project is an automated password spraying tool developed to meet the following requirements:
The ability to be deployed on several cloud platforms/execution providersThe...
© kalilinuxtutorials.com 2025





.png)