APPLICATIONS
HOT NEWS
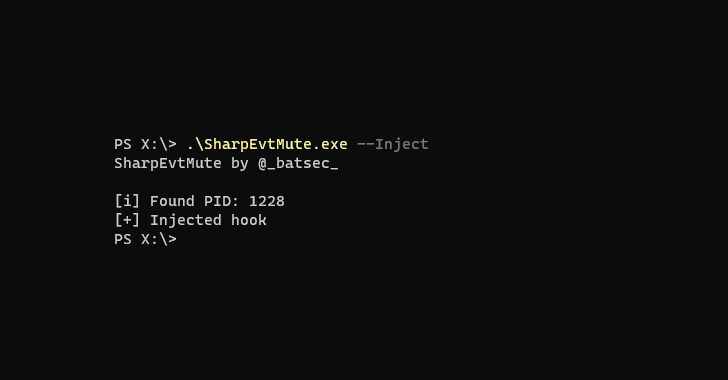
EvtMute : Apply A Filter To The Events Being Reported By...
EvtMute is a tool that allows you to offensively use YARA to apply a filter to the events being reported by windows event logging.
Usage
Grap...
© kalilinuxtutorials.com 2025