APPLICATIONS
HOT NEWS
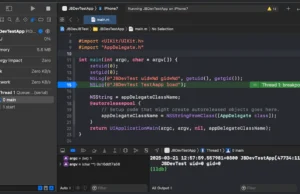
JBDev : A Tool For Jailbreak And TrollStore Development
JBDev is a specialized development tool designed to streamline the creation and debugging of jailbreak and TrollStore applications using Xcode.
It provides developers with...
© kalilinuxtutorials.com 2025