APPLICATIONS
HOT NEWS
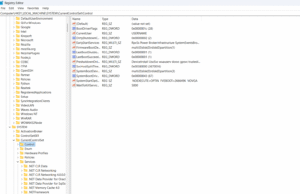
How to Use the Windows Registry to optimize and control your...
The Windows Registry Editor lets you easily view and control critical Windows system and application settings. It acts as a central hub, storing...
© kalilinuxtutorials.com 2025