APPLICATIONS
HOT NEWS
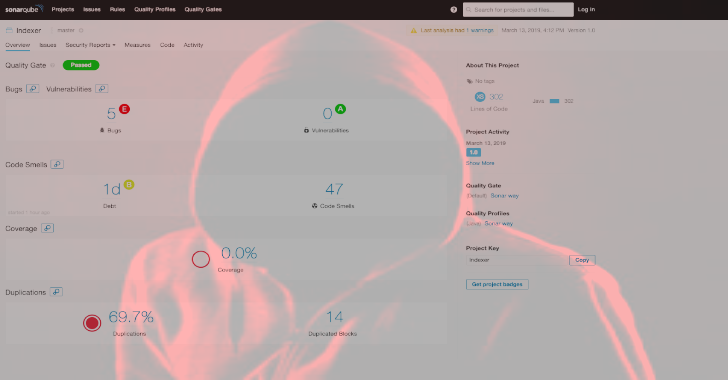
AutoSource : Automated Source Code SonarQube
AutoSource is an automated source code review framework integrated with SonarQube which is capable of performing static code analysis/reviews.
It can be used for...
© kalilinuxtutorials.com 2025






.webp)