APPLICATIONS
HOT NEWS
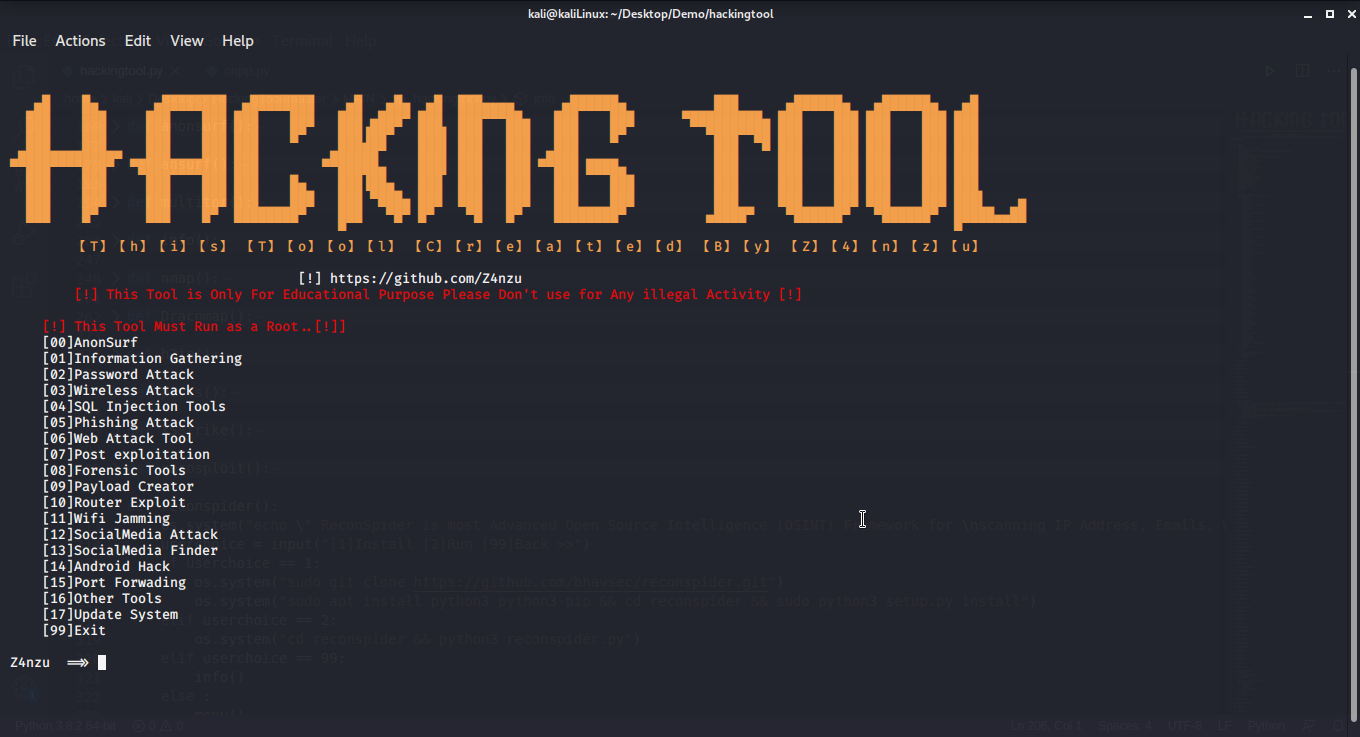
Hackingtool – All in One Hacking tool For Hacker
A hacking tool is a piece of software that can be used for different things in cybersecurity and vulnerability testing. These tools help security...
© kalilinuxtutorials.com 2025