APPLICATIONS
HOT NEWS
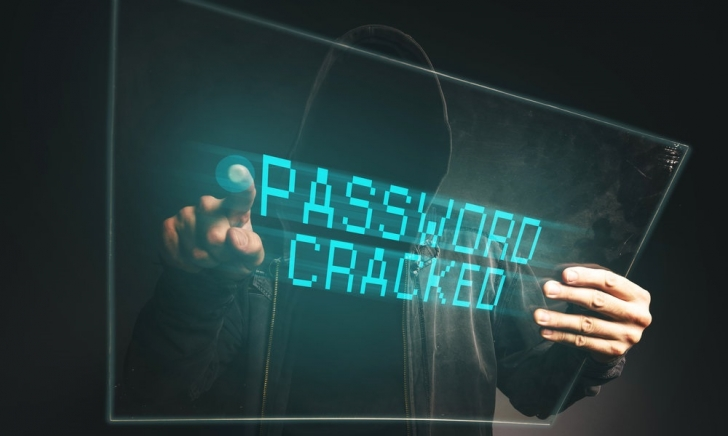
How to Protect Yourself Against Common Password Attacks
To avoid password attacks, Authentication and access management may be evolving, but passwords are not going to disappear in the near future. Experts believe...
© kalilinuxtutorials.com 2025