APPLICATIONS
HOT NEWS
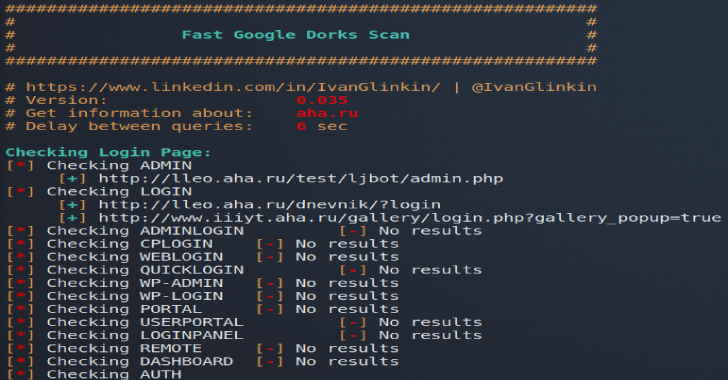
Fast Google Dorks Scan
Fast Google Dorks Scan is a script to enumerate web-sites using Google dorks.
Usage example: ./FGDS.sh megacorp.one
Version: 0.035, June 07, 2020
Features
Looking for the common admin...
© kalilinuxtutorials.com 2025