APPLICATIONS
HOT NEWS
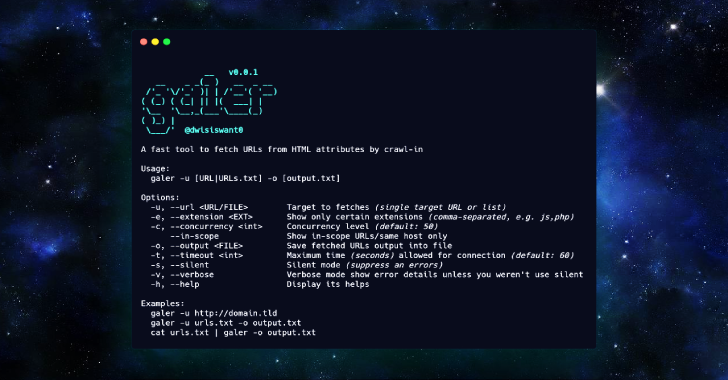
Galer : A Fast Tool To Fetch URLs From HTML Attributes...
Galer is a fast tool to fetch URLs from HTML attributes by crawl-in. Inspired by the @omespino Tweet, which is possible to extract src,...
© kalilinuxtutorials.com 2025