APPLICATIONS
HOT NEWS
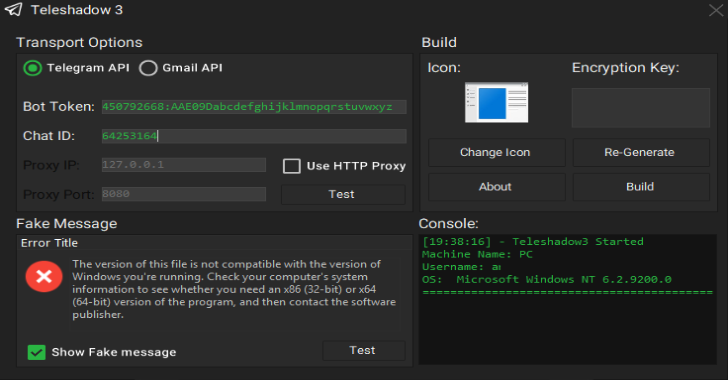
TeleShadow3 : Telegram Desktop Session Stealer (Windows)
Teleshadow3 is a advanced Telegram desktop session hijacker for windows, you can download tool by clickin here. Set the email and sender details...
© kalilinuxtutorials.com 2025