APPLICATIONS
HOT NEWS
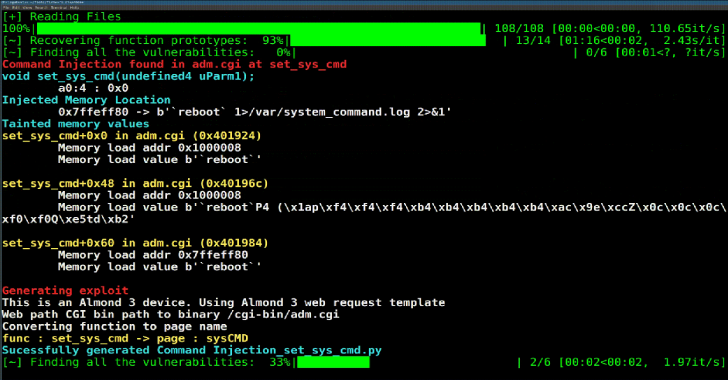
Firmware Slap : Discovering Vulnerabilities In Firmware Through Concolic Analysis &...
Firmware slap combines concolic analysis with function clustering for vulnerability discovery and function similarity in firmware. Firmware slap is built as a...
© kalilinuxtutorials.com 2025