APPLICATIONS
HOT NEWS
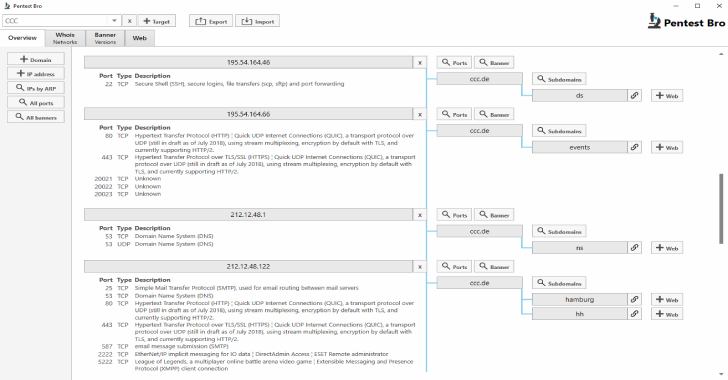
Karma v2 – The Ultimate Tool For Enhanced Cybersecurity Research
???????????????????? ???????? can be used by Infosec Researchers, Penetration Testers, Bug Hunters to find deep information, more assets, WAF/CDN bypassed IPs, Internal/External Infra, Publicly...
© kalilinuxtutorials.com 2025







.webp)