APPLICATIONS
HOT NEWS
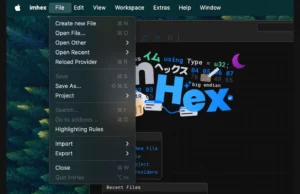
Massive UX Improvements, Custom Disassemblers, And MSVC Support In ImHex v1.37.0
The latest release of ImHex v1.37.0 introduces a host of exciting features and improvements, enhancing its usability and functionality for reverse engineers and programmers.
Massive...
© kalilinuxtutorials.com 2025