APPLICATIONS
HOT NEWS
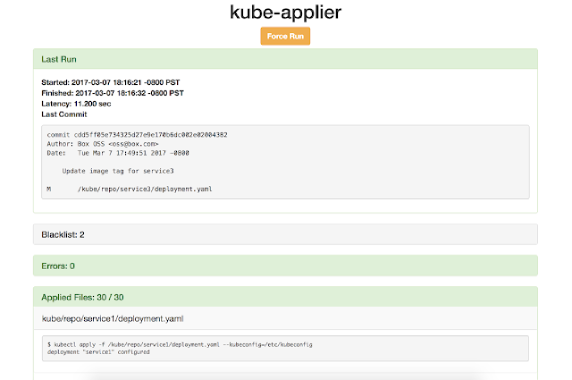
Kube-Applier : Enables Automated Deployment And Declarative Configuration For Your Kubernetes...
Kube-Applier is a service that enables continuous deployment of Kubernetes objects by applying declarative configuration files from a Git repository to a Kubernetes cluster.
kube-applier...
© kalilinuxtutorials.com 2025