APPLICATIONS
HOT NEWS
Theo : Ethereum Recon And Exploitation Tool
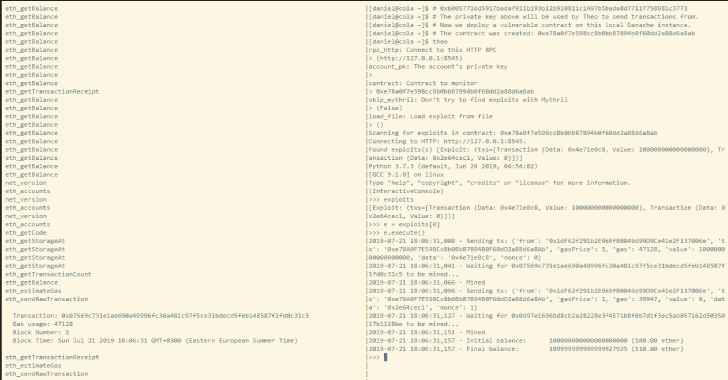
Theo aims to be an exploitation framework and a blockchain recon and interaction tool.
Features
Automatic smart contract scanning which generates a list of possible exploits.Sending...
© kalilinuxtutorials.com 2025