APPLICATIONS
HOT NEWS
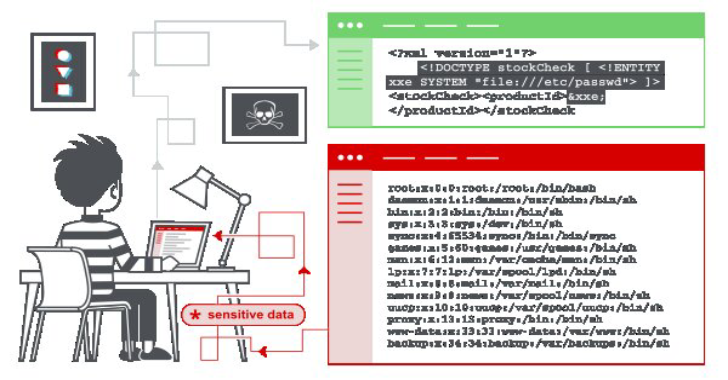
XML External Entity – XXE Injection Payload List
In this section, we'll explain what XML external entity injection is, describe some common examples, explain how to find and exploit various ...
© kalilinuxtutorials.com 2025