APPLICATIONS
HOT NEWS
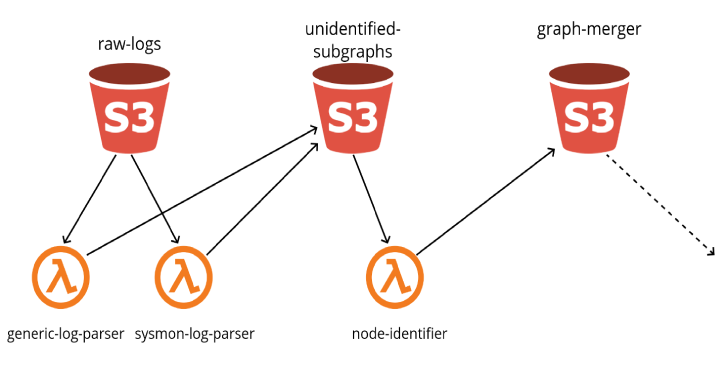
Grapl : Graph platform for Detection and Response
Grapl is a Graph Platform for Detection and Response. In short, Grapl will take raw logs, convert them into graphs, and merge those graphs...
© kalilinuxtutorials.com 2025