APPLICATIONS
HOT NEWS
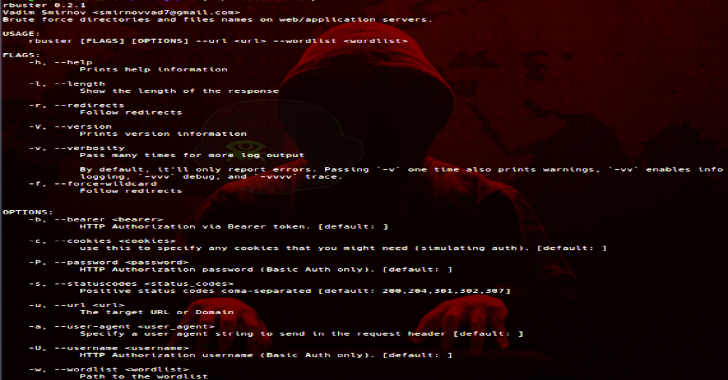
RBuster : Yet Another Dirbuster
Rbuster is yet another dirbuster with the latest version of v0.2.1. Following are the common command line options;
-a <user agent string> - specify a...
© kalilinuxtutorials.com 2025