APPLICATIONS
HOT NEWS
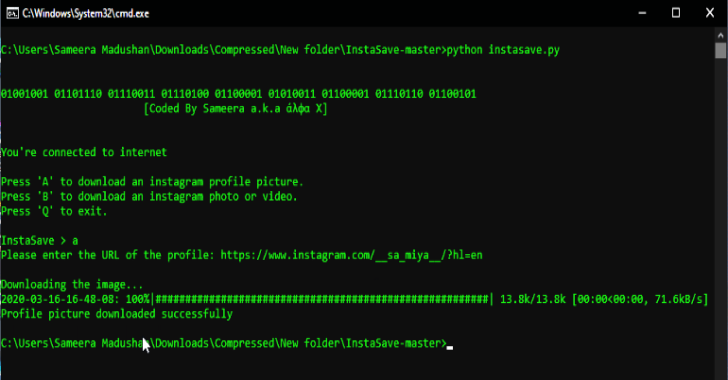
InstaSave : Python Script To Download Images, Videos & Profile Pictures...
InstaSave is a python script to download images, videos & profile pictures from Instagram without any API access.
Also Read - Pypykatz : Mimikatz...
© kalilinuxtutorials.com 2025






%20(1).png)