The journey of reading 10,000 disclosed HackerOne (H1) reports offers valuable insights into the bug bounty ecosystem, emphasizing the importance of analyzing real-world vulnerabilities.
This ambitious project was undertaken to deeply understand the types of bugs being reported, accepted, or rejected, and to refine strategies for bug bounty hunting.
Here’s a breakdown of how this goal was approached and the tools used.
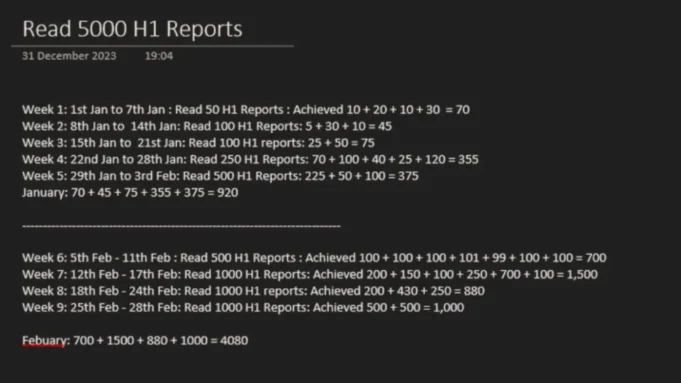
The primary aim was to analyze disclosed bug reports to identify patterns in vulnerabilities and reporting. Initially targeting 10,000 reports, the researcher capped it at 5,000 after recognizing recurring trends.
The process spanned nine weeks (approximately 60 days), with an average of 125 reports read daily, totaling nearly 99 hours of focused study.
This deep dive into disclosed reports helped uncover common vulnerabilities and reporting practices.
Tools And Methods
To collect the disclosed reports efficiently, the researcher utilized a Python script to interact with HackerOne’s GraphQL API. Here’s how it worked:
- Intercepting Requests: The researcher intercepted requests to HackerOne’s Hacktivity page.
- Iterative Querying: By modifying parameters like
limitand iterating through report pages in steps of 25 or 50, they gathered JSON responses containing report details. - Data Processing: The JSON data was parsed to extract report IDs and URLs.
- Automation: A Python script automated this process, saving report URLs into a text file for further analysis.
Here’s a snippet of the Python script used:
import requests
import json
j = 0
while j < 20000000:
graphql_query = {
"operationName": "HacktivitySearchQuery",
"variables": {
"queryString": "*:*",
"size": 25,
"from": j,
"sort": {"field": "disclosed_at", "direction": "DESC"}
},
"query": "query HacktivitySearchQuery..."
}
response = requests.post('https://hackerone.com/graphql', json=graphql_query)
if response.status_code == 200:
data = response.json()
with open('h1reports.txt', 'a') as f:
for i in data["data"]["search"]['nodes']:
f.write(i['report']['url'] + '\n')
else:
print(f"Request failed with status code: {response.status_code}")
j += 25Key Insights
- Common Vulnerabilities: Patterns in vulnerabilities such as XSS, IDOR, and CSRF were identified.
- Report Quality: High-quality reports include clear descriptions, proof-of-concept (PoC), and reproducible steps.
- Efficiency in Analysis: Automating data collection saved significant time and allowed for a systematic review.
This exercise highlights the value of studying disclosed reports to improve vulnerability discovery skills. It underscores the need for clear report writing and understanding program scopes to maximize success in bug bounty programs.
By leveraging tools like APIs and automation scripts, researchers can efficiently gather insights from publicly available data, enhancing their expertise in ethical hacking and vulnerability reporting.





.jpg)





%20(1).png)