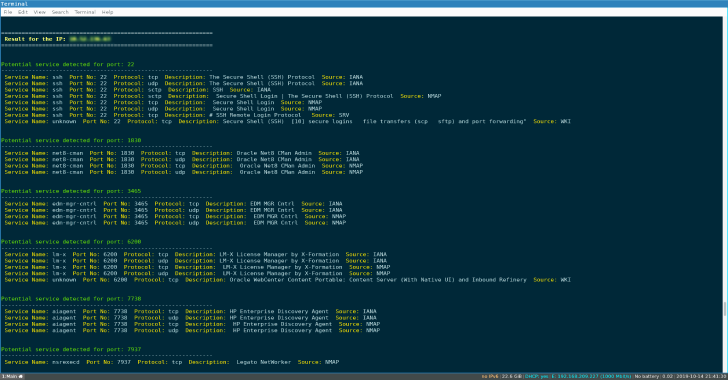
OFFPORT_KILLER tool aims at automating the identification of potential service running behind ports identified manually or on services running locally only.
The tool is useful:
- When nmap or any scanning tool is not available and in the situation during which you did a manual port scanning and then want to identify the services running behind the identified ports and
- also if you have been able to identify services running locally via (netstat, running processes SNMP or else).
Several databases are used such as the one from NMAP, IANA and linux machines.
The tool can be used by pentesters, system admins, CTF players, students, System Auditors and trolls :).
Usage
- Example
./OFFPORT_KILLER.sh -i inputfile.txt -r report.txt -e /tmp/
Arguments
- -i : input file (format IP:PORT)
- -r : report name (save the output)
- -h : help
Steps
- Step 1: Peform a manual port scanning (using nc, tcpdump or whatever) or identify services running locally
- Step 2: Create a file with format IP:PORT (where IP is the target IP address and PORT is a port identified).
- Step 3: Run the tool with the file created using the argument -i
Note: Create an entry for each port, several IP can be input in the file.
inputfile.txt
192.168.1.12:1830
192.168.1.12:7738
192.168.1.14:22
192.168.1.14:7738
192.168.1.15:3465
Read Output
To read output while keeping the aspect (color), especially when cat is not adequate and the output is too long.
- less -R report.txt
Disclaimer
This script is for Educational purpose ONLY. Do not use it without permission. The usual disclaimer applies, especially the fact that me (TH3xACE) is not liable for any damages caused by direct or indirect use of the information or functionality provided by these programs. The author or any Internet provider bears NO responsibility for content or misuse of these programs or any derivatives thereof. By using these programs you accept the fact that any damage (dataloss, system crash, system compromise, etc.) caused by the use of the script is not my responsibility.









%20(1).png)
