EarlyCascade is a cutting-edge process injection technique developed by Outflank to evade modern Endpoint Detection and Response (EDR) systems.
This method operates during the early stages of process creation, injecting and executing malicious code before EDRs initialize their user-mode detection measures.
By leveraging the Shim engine and hijacking its callback, EarlyCascade achieves stealthy execution while minimizing detection risks.
Key Features Of EarlyCascade
- Shim Engine Exploitation: The technique forces the Shim engine to activate, enabling the hijacking of the
g_pfnSE_DllLoadedcallback inntdll.dll. This callback is manipulated to execute malicious code during process initialization without triggering Loader Lock restrictions. - Stealth and Efficiency: Unlike traditional methods such as Early Bird APC Injection, EarlyCascade avoids cross-process Asynchronous Procedure Calls (APCs), reducing remote process interaction and leaving a minimal footprint. This makes it highly effective against advanced EDRs.
- Timing Advantage: EarlyCascade intervenes in the Windows process creation flow at a critical moment before EDR detection mechanisms are fully operational. This precise timing allows it to bypass security measures seamlessly.
Steps In The EarlyCascade Process
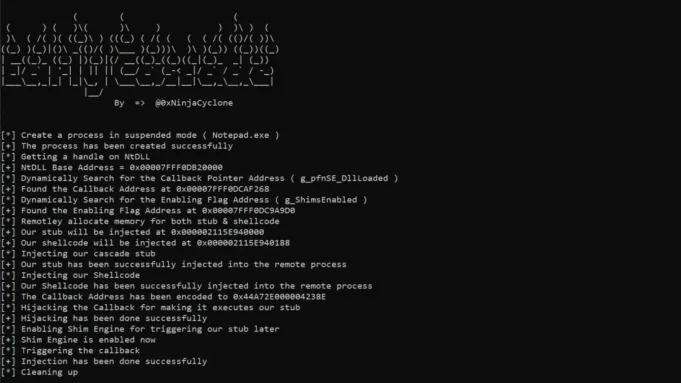
- Process Creation: A target process is created in a suspended state.
- Memory Allocation: Addresses for enabling flags (
g_ShimsEnabled) and callbacks (g_pfnSE_DllLoaded) are located dynamically, and memory is allocated for the shellcode. - Callback Hijacking: The Shim engine is enabled by setting
g_ShimsEnabledto true, and theg_pfnSE_DllLoadedpointer is overwritten with the shellcode address. - Execution Trigger: The process thread is resumed, triggering the callback.
- Shellcode Execution: The shellcode disrupts detection measures, disables the Shim engine to prevent crashes, and queues an Asynchronous Procedure Call (APC) for further execution.
EarlyCascade represents a significant advancement in evasion techniques, challenging even top-tier EDRs by exploiting timing and reducing suspicious behavior.
Its ability to bypass traditional detection methods highlights the evolving sophistication of adversarial tactics in cybersecurity.







.jpg)




