Xkeys is a Burp Suite extension designed to extract interesting strings such as keys, secrets, and tokens from web pages. It operates as a passive scanner, identifying these strings and listing them as information issues within Burp Suite.
This article will delve into the setup, usage, and functionality of the Xkeys extension.
Setup And Requirements
To use Xkeys, you need to set up a Python environment in Burp Suite by providing the Jython.jar file. Here are the steps:
- Download Xkeys: Obtain the BurpSuite-Xkeys.zip file.
- Install Extension: In Burp Suite, go to the ‘Extensions’ tab under ‘Extender’, select ‘Add’, and choose ‘Python’ as the extension type. Provide the path to the “Xkeys.py” file.
- Requirements: Ensure you have Jython 2.7.0 and Burp Suite Pro installed.
Once installed, Xkeys will start identifying assets through a passive scan.
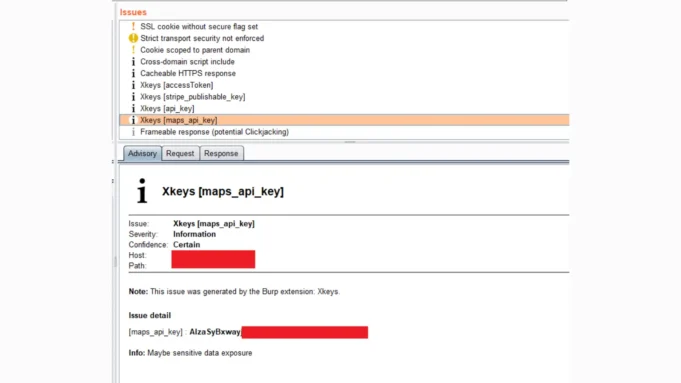
It searches for strings in various formats, such as {keyword}=<value>, {keyword} = <value>, {keyword}'='<value>', etc., and reports them as issues in the Burp Suite interface.
Xkeys can extract values from a wide range of formats, including but not limited to:
- Key-Value Pairs:
{keyword}=<value>,{keyword} = <value>,{keyword}'='<value>',{keyword}"="<value>" - Colon Separated:
{keyword}:"<value>",{keyword}": "<value>"
These extracted values are displayed in the issues box and output extender within Burp Suite.
Xkeys is beneficial for security testing and bug bounty hunting by helping identify potential security issues related to exposed secrets or tokens.
The extension credits include PortSwigger’s example-scanner-checks and RedHuntLabs’ BurpSuite-Asset_Discover, with contributions from the Sec7or Team and Surabaya Hacker Link.
In summary, Xkeys is a valuable tool for web application security testing, providing insights into potentially sensitive information exposed on web pages.






.jpg)


.webp)
.webp)
