XSHOCK Shellshock Exploit. All founded directories will be saved in vulnurl.txt file. The results of the executed commands are saved in response.txt.
Features
This tool include:
- CGI VULNERABILITY
- DIRECTORY SCAN
- RUN COMMAND WITH FOUNDED CGI
- SHOW VULNERABLE URLS
- UPDATE PROXY
Installation
git clone https://github.com/capture0x/xShock/
cd xShock
pip3 install -r requirements.txt
Also Read – Token Reverser : Word List Generator To Crack Security Tokens
Usage
python3 main.py
CGI VULNERABILITY
Checks cgi-bin directory on the target site
- e.g:http://targetsite.com
DIRECTORY SCAN
This works with wordlists. Scans url on the target site. Important notice: Please enter full path of wordlist after the url.(Not file. It should be directory)
- e.g: http:// targetsite.com/cgi-bin/selectedworlist
- e.g: http://targetsite.com/cgi-bin /usr/share/wordlists/dirb –> This is directory of wordlist. Not file!
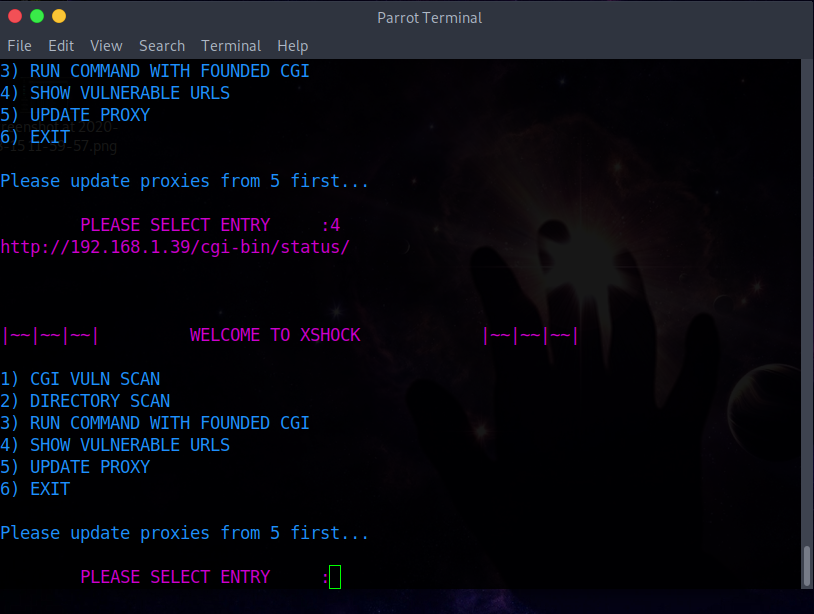
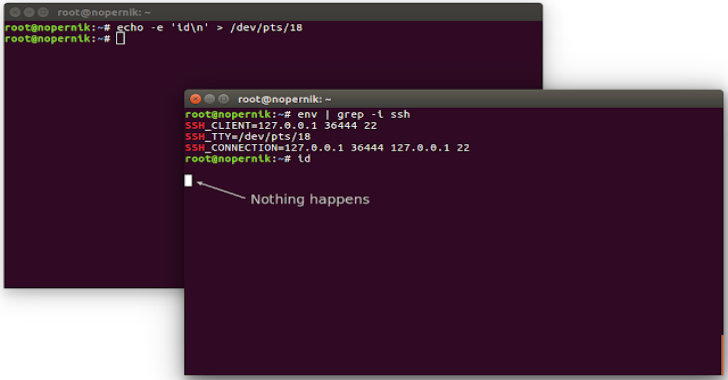
RUN COMMAND WITH FOUNDED CGI
By entering the url in the vuln.txt file, you can try running commands in the found urls.
http://targetsite.com/cgi-bin/status
SHOW VULNERABLE URLS
Shows founded urls in vuln.txt file.
UPDATE PROXY
You can update proxies from web manually.
How to use?
Screenshots