APPLICATIONS
HOT NEWS
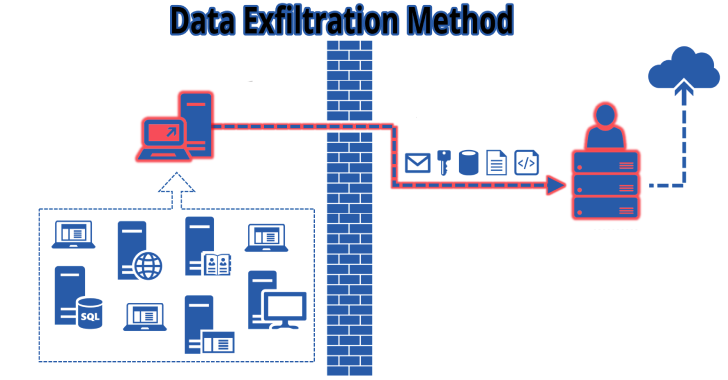
Lollipopz : Data Exfiltration Utility For Testing Detection Capabilities
Lollipopz is a data exfiltration utility for testing detection capabilities. Data exfiltration utility used for testing detection capabilities of security products. Obviously for legal...
© kalilinuxtutorials.com 2025