APPLICATIONS
HOT NEWS
Minimalistic Offensive Security Tools
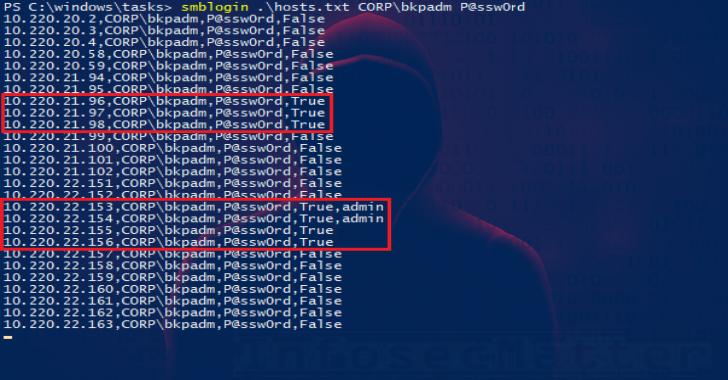
Minimalistic is a simple SMB login attack and password spraying tool.
It takes a list of targets and credentials (username and password) as parameters...
© kalilinuxtutorials.com 2025






.webp)
.png)


.webp)