APPLICATIONS
HOT NEWS
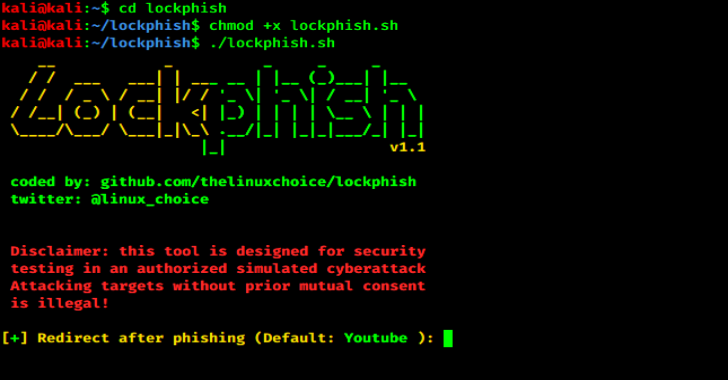
Lockphish : The First Tool For Phishing Attacks
Lockphish it's the first tool (07/04/2020) for phishing attacks on the lock screen, designed to grab Windows credentials, Android PIN and iPhone Passcode using...
© kalilinuxtutorials.com 2025